Technology is evolving at a rapid pace and is constantly transforming. Cyberthreats are evolving, too, so organizations must continue to be vigilant and seek new ways to improve their cybersecurity posture.
In this article, we’ll discuss the five steps companies of all sizes can take today to make their data impregnable. By adopting these strategies, you can rest assured that you are keeping up-to-date with the shifting sands of the threat landscape. (Also read: Threat Hunting: 7 Ways to Reduce Risk.)
1. Use A Password Manager
An on-premise password manager, like the Password Depot Enterprise Server, is essential for safeguarding your credentials and data. Password managers provide a secure, encrypted repository for all your passwords and allow you to create complex and unique passwords for each account without having to remember them all.
With a password manager, you can easily take care of multiple accounts, share passwords with trusted contacts and receive alerts about suspicious activity. Additionally, password managers often have features such as two-factor authentication and auto-fill capabilities.
Using a password manager ensures that your precious access credentials remain locked away, protecting your business from a data breach.
2. Encrypt All Files
Encryption scrambles data, making it unreadable to anyone who doesn’t have the decryption keys. With encryption, you can keep your data safe from malicious actors and reduce the risk of a data breach. (Also read: 10 Biggest Data Breaches of All Time – And How to Prevent Them.)
Thus, data encryption is an essential part of any cybersecurity strategy. Whether data is in transit or at rest, encryption is a must-have for any organization that wants to protect its data and reduce the risk of a data breach.
3. Implement Multi-Factor Authentication
Multi-factor authentication (MFA) is a security process requiring more than one form to verify a user’s identity. It typically involves a combination of something the user knows (like a password), something the user has (like a phone or security token) and something the user is (like a biometric identifier).
Think of MFA as a three-pronged approach to keeping your data secure. It’s like having a security guard at the door of your digital world, checking IDs and verifying who you are before letting you in. It’s an additional step that can take a few extra seconds, but it’s worth it for the added peace of mind that comes with knowing your valuable information is protected.
If you value your data, make sure to use multi-factor authentication whenever possible.
4. Back Up Your Data
Applying backup processes ensures that if something goes wrong, you have a process in place that enables you to recover and get back on track.
For example, in the event of a ransomware attack, a corrupt storage device or loss of equipment, your organization can call on a backup of valuable data to restore your information and get back on track. (Also read: Data Breach Response: 5 Essential Steps to Recovery.)
There are several ways to back up your data, such as using software, a physical backup device, or cloud-based services. Some options for backing up your data include:
-
Software backup solutions. These are the most popular option for backing up data because they are easy to use and manage. They can be installed on a server or computer.
-
Physical backup devices. Another popular option, physical backup devices are typically large, rectangular boxes that store data on physical media, such as a hard drive, tape or solid state drive (SSD). Physical backup devices can be transported to an off-site location.
-
Cloud-based backup services. These offer a convenient way to back up your data. They can be used to back up data to a remote server or to back up data to a cloud storage service, such as AWS, Google Drive, iCloud, or Microsoft OneDrive.
Some password managers, like the Password Depot Enterprise Server, allow you to back up your password databases and sync your data to access it from any device.
5. Implement the Basics of Cybersecurity
It’s majorly important that an organization has the basics of security in place. This is a set of fundamental principles that can help protect businesses from the most common cyberthreats.
Cybersecurity principles serve as the basic framework for keeping your networks and data unassailable. Without them, you risk leaving your organization vulnerable to malicious actors who could take advantage of any weaknesses in your systems or applications.
Basic cybersecurity principles include:
-
Servers: Make sure server settings are as secure as possible.
-
Firewalls: Regular inspection of firewall rules is a must.
-
Internet gateways: Review rule sets quarterly.
-
Access control: On a need-to-know, and just in time (JIT) basis.
-
AV & malware: Apply signature updates as soon as possible.
-
Patch management: Apply updates to your servers and desktops.
Finally, ensure all default usernames, passwords and parameters have been changed from those provided by the manufacturer. Each element is essential for keeping your networks and data free from cyberthreats. (Also read: Cybersecurity 101.)
Why is Enterprise Cybersecurity Important?
Enterprise cybersecurity solutions protect a company’s data and resources from malicious activities. Threats, such as malware, viruses and other cyber-attacks, can take many forms. Strategic solutions can protect a company’s data from these threats by detecting and blocking them before they cause damage.
Typically, an enterprise will employ traditional control techniques of protecting data locally, then extend the scope of controls to protect data transfers across public networks and endpoint devices. Use perimeter firewall defenses only to allow safe traffic in and out of the network.
Additionally, Web Application Firewalls (WAFs) can be used to prevent attacks like those listed in the OWASP Top 10. Advanced systems will be implemented to detect and block unwanted incursions, achieved by deploying Intrusion Detection Systems (IDS) and Intrusion Prevention Systems (IPS).
In addition to standard threats such as Distributed Denial-of-Service (DDoS) attacks, social engineering attacks and software vulnerabilities, operational enterprise cybersecurity addresses many other complex problems.
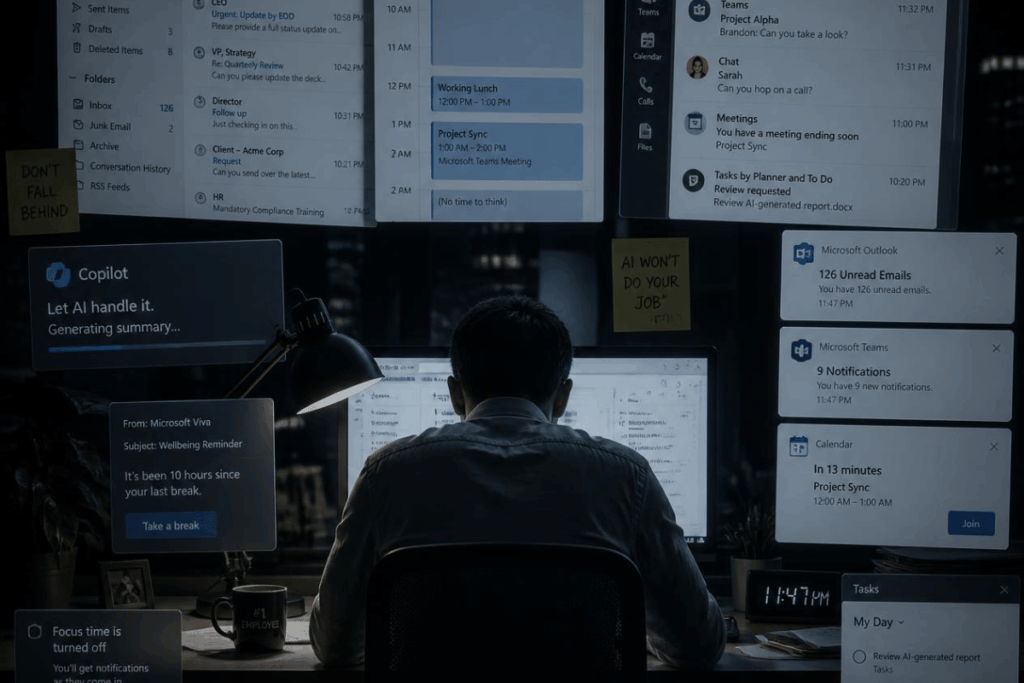
Because many internal and external applications and systems require a username and password to access, an enterprise password manager is duly important. Gone are the days when you could write these down on a post-it note and stick them on the side of the monitor!
Conclusion
Using a password manager, encrypting your data, implementing multi-factor authentication, backing up your data and employing basic principles of cybersecurity are crucial steps to keeping your organization’s data safe.
Cybersecurity solutions like the Password Depot Enterprise Server allow you to target several of these steps at once, which can result in time savings, increased efficiency and — most importantly — complete control over your organization’s cybersecurity. To learn more about Password Depot, visit their website.