Say you’ve met someone on a dating site, a really charming someone – the perfect romantic partner. And let’s say the relationship blossoms over the next few months. Things are going really well. In fact, you’ve fallen hard for this person.
Then, this person gives you a sad story about their financial problems and asks you to send them some cryptocurrency to help them through this difficult time. Or maybe, they tell you about this great crypto investment opportunity and ask you to invest. Of course, you don’t hesitate because — after all — you and this individual are soulmates.
But after you send them the crypto, you never hear from them again. So much for romance.
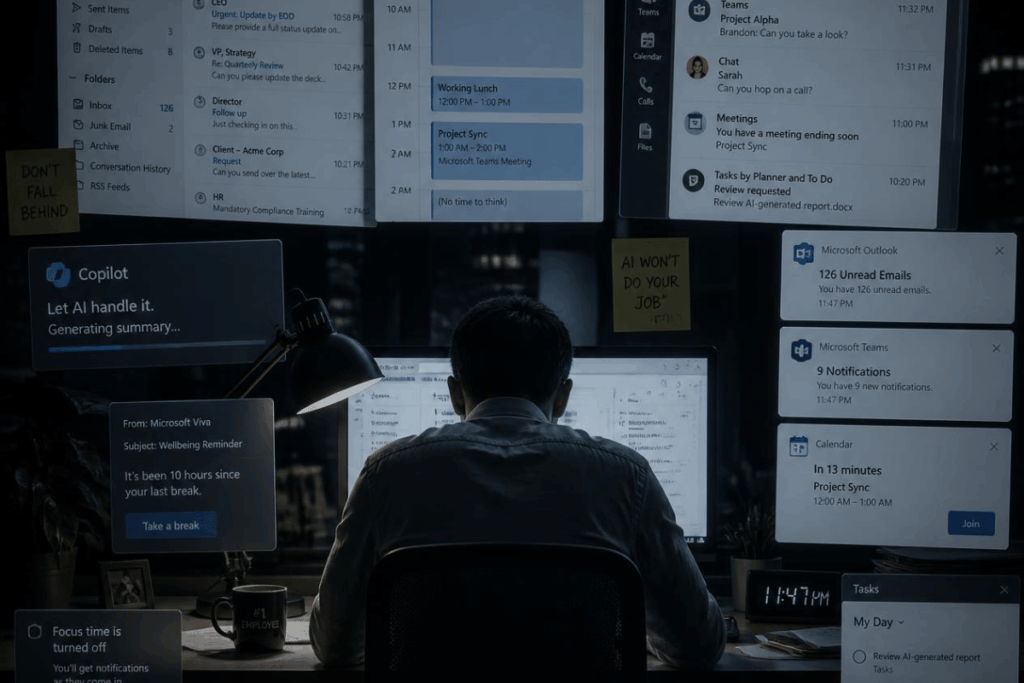
If you think you’re too smart to fall for this type of scam, think again. Adam Levin, a cybersecurity, privacy, and identity theft expert, says: “We’ve had somebody on our podcast, ‘What the Hack With Adam Levin,’ who lost more than $450,000 to a romance scam that blossomed into a cryptocurrency investment opportunities scam.”
Techopedia sits down with Levin to discuss how you can protect your data, your identity, and your money from cyber criminals and steer clear of such scams. Welcome to the “Three M”s of cybersecurity — minimizing your risk, monitoring your accounts, and managing the damage.
Key Takeaways
- Many of the scams — from romance scams to identity theft — have been around for years, it’s just the methods or technology have changed.
- Keep your finances safe by keeping a close eye on your financial accounts, looking for anything that looks unusual or unfamiliar.
- Having a strong credit portfolio and a strong identity portfolio will give you the opportunity to build a safety net because more money will be available to invest.
- A number of organizations offer programs with professional fraud experts to help you through an identity incident so you’re not alone.
About Adam Levin
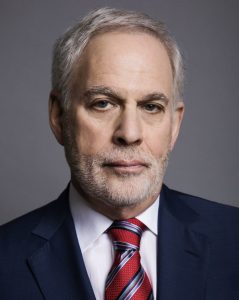
Adam Levin is a consumer affairs advocate and serial entrepreneur with more than 40 years of experience. He is an internationally recognized expert on cybersecurity, privacy, identity theft, fraud, and personal finance.
Levin is the author of “Swiped: How to Protect Yourself in a World Full of Scammers, Phishers, and Identity Thieves.” He hosts a weekly podcast, “What the Hack with Adam Levin,” with co-hosts Beau Friedlander and Travis Taylor. The podcast features guests and experts who discuss their experiences with scams, identity theft, privacy, and other cyber-related issues.
Throughout his career, Levin’s mission has been to educate consumers, businesses, law enforcement officials, and lawmakers about consumer privacy, identity management and protection, credit, as well as election security issues.
A highly sought expert, Levin has testified before state and federal regulators as well as legislative committees on his areas of expertise. He routinely addresses cybersecurity, financial services, insurance, educational, and law enforcement organizations throughout the United States and Europe.
Protect Yourself From Online Scams
Q: What are the scams that allow criminals to steal people’s money?
A: There are a few. For example, there are romance scams, tech support scams, cryptocurrency scams, and the ‘pig-butchering’ scams that actually play into the cryptocurrency scams.
With a tech support scam, you think you’re communicating with a technology company, but you’re actually communicating with scammers. And you let them into your computer, either you download something or they find a way in with you on the phone. And then they’re supposedly resolving the issue in your computer, but what they’re really doing is sucking out every possible piece of data they can while they’re in your computer.
And then the whole theory of pig butchering [which alludes to the way in which hogs are ‘fattened’ up before they are butchered] is that the scammer contacts someone via an SMS text message and pretends they contacted the individual by mistake. But it’s not a mistake.
From then on, the scammer develops a relationship with that individual. Eventually, the scammer gets the person interested in an investment opportunity in cryptocurrency, for example.
The individual agrees, and the scammer explains which crypto app to acquire, but it’s usually a fake platform.
“Soon, the amounts in the account seem to be going up and up and up, and the scammer gets the individual to contribute more and more and more. At some point, the individual wants to take some money out, but the scammer convinces them not to.”
Eventually, the scammer makes it appear as if the crypto stock has plummeted or the individual can’t access the crypto platform, and the scammer disappears with their money. Finally, it dawns on the individual that they’ve been taken for a ride.
“Similarly, romance scams involve a person finding who they think is the perfect partner on a dating site. Things are going well, and the conversation is great until that person either asks for crypto because they’re experiencing financial trouble or tells the victim to invest in a new platform. Both usually lead to lost funds, bruised egos, and empty pockets.”
We’ve had somebody on our podcast, ‘What the Hack With Adam Levin,’ who lost more than $450,000 to a romance scam that blossomed into a cryptocurrency investment opportunities scam. And a retired attorney who was on the show lost more than $600,000 to a tech support scam.
Q: What do people need to do to keep their finances safe from cybercrime?
A: First, you have to keep a close eye on your financial accounts, looking for anything that looks unusual or unfamiliar.
You should check all your accounts on a daily basis. If you’re more interested in a laid-back approach, you can sign up for free with your bank, credit union, or credit card company for something called transactional monitoring. And that’s where anytime there’s a transaction in your account, you’re notified.
“You can also freeze your credit, which stops someone dead from trying to get access to your credit to open new accounts. None of these are 100% effective, but they make you a harder target.”
On the Three Portfolio Theory
Q: What is your ‘three portfolio’ theory?
A: When most people hear the word portfolio, the Pavlovian response is investments. The truth is in life we have other portfolios. We also have educational portfolios and health-related portfolios, for example.
“But in addition to your investments, the two biggies are your credit and your identity. And where you would get a professional manager to manage your investment portfolio, you need to be the professional manager of your credit and identity portfolios.”
You have to build them, manage them, nurture them, and protect them. If anything goes wrong with your identity portfolio, it can definitely impact your credit portfolio.
And then, if you’re in trouble with your credit portfolio, you’re going to have to draw on whatever money you have available, which could impact your investments, assuming you even have enough money to make investments.
However, having a strong credit portfolio and a strong identity portfolio will give you the opportunity to build a safety net because more money will be available to invest.
How To Ensure Your Personal Data Stays Safe
Q: Will the increase in the use of artificial intelligence help or hurt consumers?
A: That’s a double-edged sword. AI is making criminals much more effective in terms of the phishing-related attacks that they do. However, AI also makes the threat assessment and analytical tools for companies more effective as well because they can detect threats more quickly.
Q: What routines should people adopt to ensure their personal data stays safe?
A: Beau Friedlander, the co-host of my podcast, and I created a framework that we call the ‘Three M’s. This is how you protect your identity portfolio and your finances and minimize your risk of exposure or reduce your attackable surface.
So how do you minimize your risk or exposure, how do you monitor your accounts so you effectively know you’re having a problem as quickly as possible, and then how do you manage the damage?
You can minimize your risk of exposure by ensuring that you’re using long and strong passwords and are not sharing them across your universe of websites. Or you can get a password manager that uses two-factor authentication. This adds an extra layer when you log in, and it also notifies you if someone else is attempting to log in.
“Also don’t authenticate yourself to someone who contacts you claiming to be your bank, for example. If you call them and they ask you to authenticate yourself, that makes sense.”
Also you should ensure that you’re operating over secure networks. When you make any sensitive transactions, be sure to use a VPN, do not use public Wi-Fi.
And if you’re connecting to a network somewhere, make darn sure it’s the real network as opposed to a trumped-up network that was created by somebody sitting two tables over from you who’s a hacker.
“When you set up security questions and answers, [make them up]. If they ask you for your mother’s maiden name, invent a name. If they ask where you went to high school, invent a name for that as well. You’re not applying for a security clearance with the federal government, where they’re going to do a background check.”
These websites just want to see if you give them the same answer that you gave when you first signed up.
And freeze your credit – It’s free. The beauty of credit freezing is that you do it with each bureau individually. Depending on the credit that you’re seeking, other than for mortgages where they pull reports from all three credit bureaus, most lenders only pull from one bureau.
So you just ask them which credit bureau they’re going to use and then unfreeze it and freeze it back when the lender is finished.
The second M is monitoring. Check your credit report religiously and look for things that don’t make sense, such as an address where you’ve never lived. Sign up for transaction alerts and sign up with credit monitoring services that do credit monitoring and identity monitoring.
Look for programs that offer both dark web monitoring and instant alerts. Do a personal privacy inventory on yourself, which is Google yourself, and see what shows up. Go to the website Have I Been Pwned, which is a free database of breached accounts. You can enter your email address or your phone number and it will tell you if it has been compromised.
And third, manage the damage. A number of organizations, such as your insurance company and your financial institution, have programs available with professional fraud experts to help you through an identity incident — so you’re not alone.
Trends in Cyberattacks
Q: What are the trends that you’re seeing in cyberattacks? What’s changed over the years?
A: It’s almost like you have to put this in the context of ‘the same music, different lyrics’ as a lot of scams haven’t really changed. It’s just that ransomware is getting worse, and international crime syndicates have now entered the romance scam arena, big time.
It’s the same with tech scams and pig butchering, which oftentimes is a combination of romance scams and cryptocurrency scams. It’s insane what’s going on.
“It’s the same imposter scams, tax scams, IRS scams almost every day. It’s like what we were used to over the years, and all the scammers do is sometimes change the facts a little bit to make you think it’s something new.”
During COVID, it was tracking scams, vaccine scams, and job opportunity scams. And with AI, the scammers are just becoming better at it. You don’t see typographical or grammatical errors; you don’t see logos with colors that look off.
Q: How are criminal syndicates stealing money using sextortion scams? What are those scams and what happens to victims?
A: Sextortion scams start off innocently enough. And we had one episode on our show about a high school student from Michigan who was the victim of a sextortion scam and committed suicide.
The scammers used hacked social media accounts to pose as young women to lure in young males. This student thought he was communicating with a young woman, and she sent him what appeared to be a compromising picture.
“She then convinces him to send her a compromising picture. Then suddenly, he receives a DM saying, “Unless you pay us $1,000, we’re going to release this picture to everybody you know, your friends, your family. And oh, by the way, here’s a collage of people you communicate with on social media.”
The teen scraped together $300 and sent it to the scammers immediately. They said it wasn’t enough, and they badgered him for another hour. He finally told them if they didn’t stop, he was going to kill himself. The scammers said they’d help him do it. And the boy did kill himself.
But there’s a just ending that’s in process right now as the FBI, working with Interpol and Nigerian intelligence, managed to track down these guys. And two of them were extradited to the United States and they’re being prosecuted in Michigan.
So, with a sextortion scam, you’re lured in by the siren song of a beautiful profile picture. And, again, it starts off innocently enough.
“But the scammers are casting a wide net and when someone responds, they immediately seize on it. And it’s not like you’re communicating with one person, you’re actually communicating with a group of people, a syndicate. And the results can cause serious psychological and financial damage and even suicide.”
Q: What do you do to keep your finances safe that can help others do the same?
A: Well, first of all, I’m by nature and profession paranoid. Therefore, I freeze my credit. However, I did confess on the show [last year] that I actually had just frozen my credit after spending a decade talking about credit freezes. And that was because [I had a false sense of security because of who I am].
But I did freeze my credit, and I monitor my accounts daily, which drives my wife crazy. I get my credit reports from the three credit bureaus, and I track my credit scores. And then I use the three Ms religiously. Because I always say whatever the cost is proactively and whatever the time suck is, it’s nothing compared to the cost or the time suck if you become a victim.